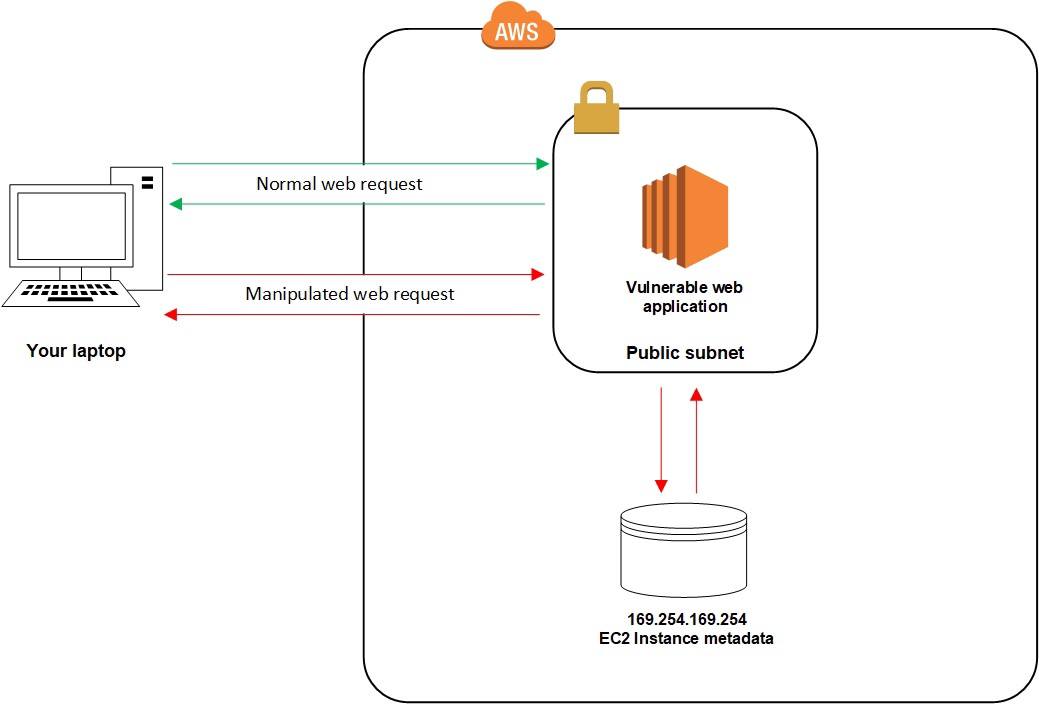
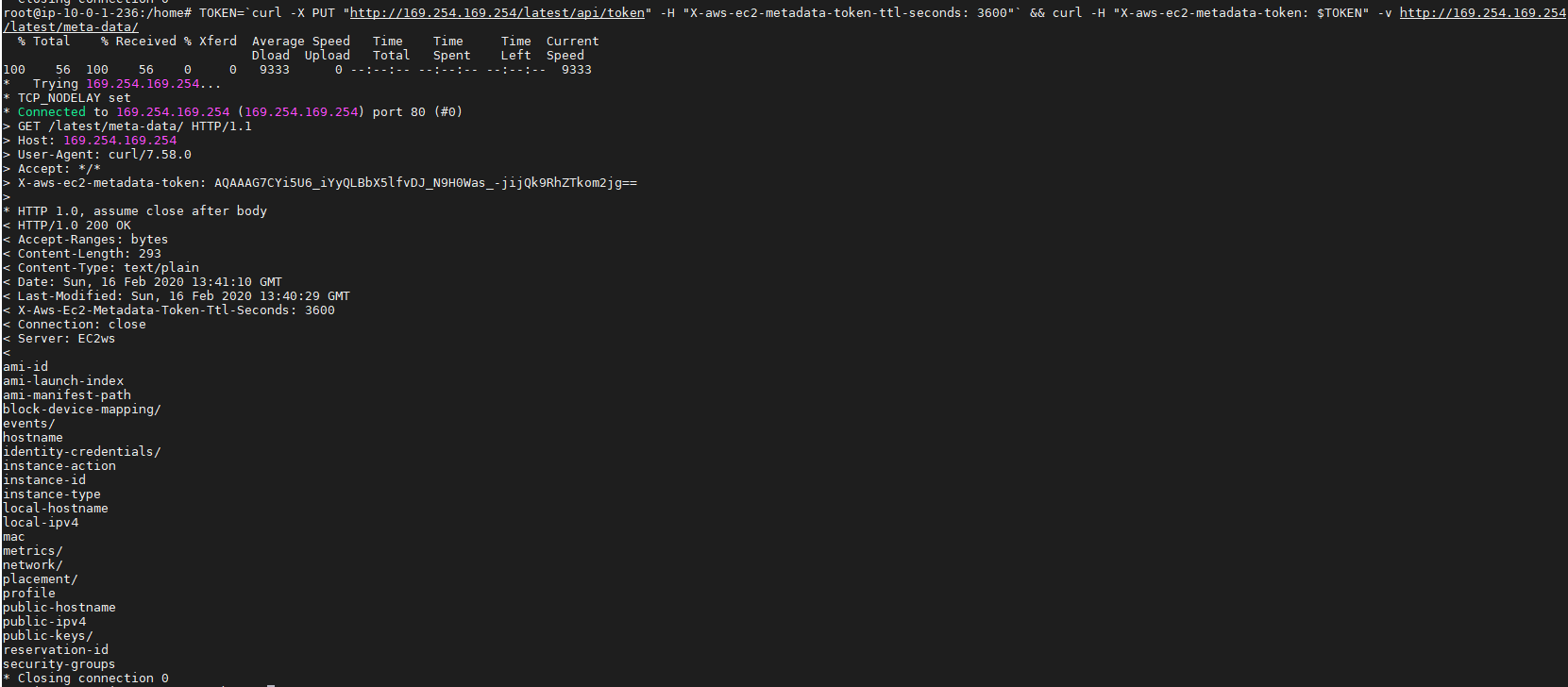
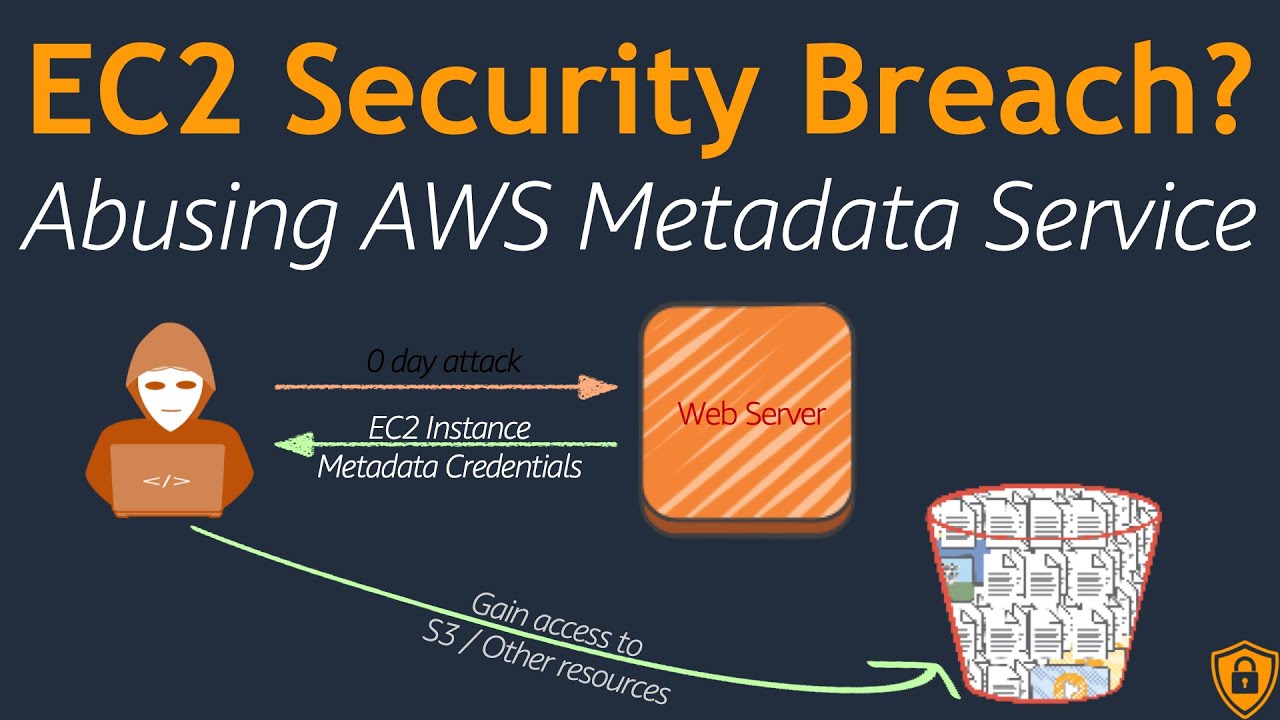
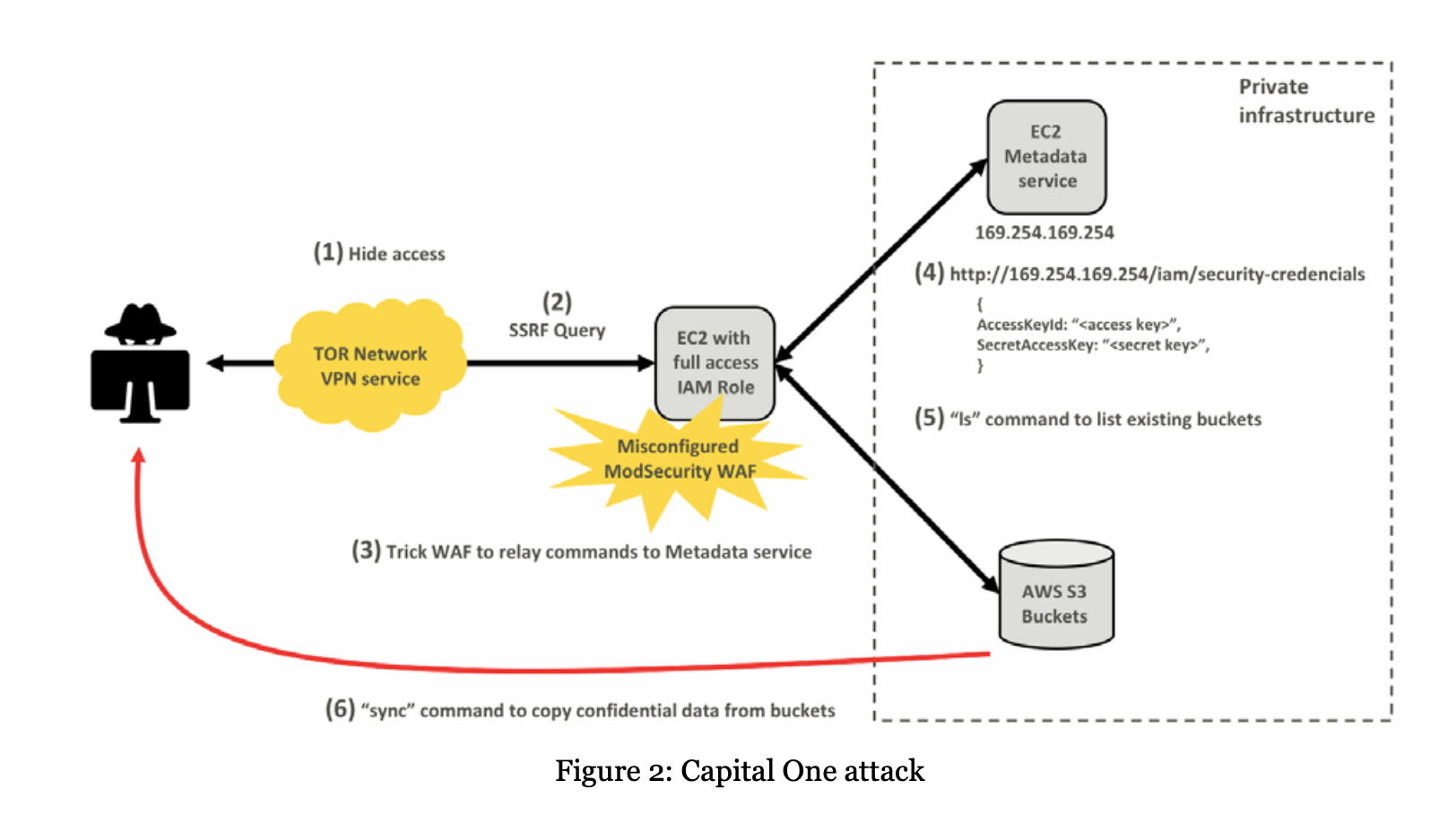
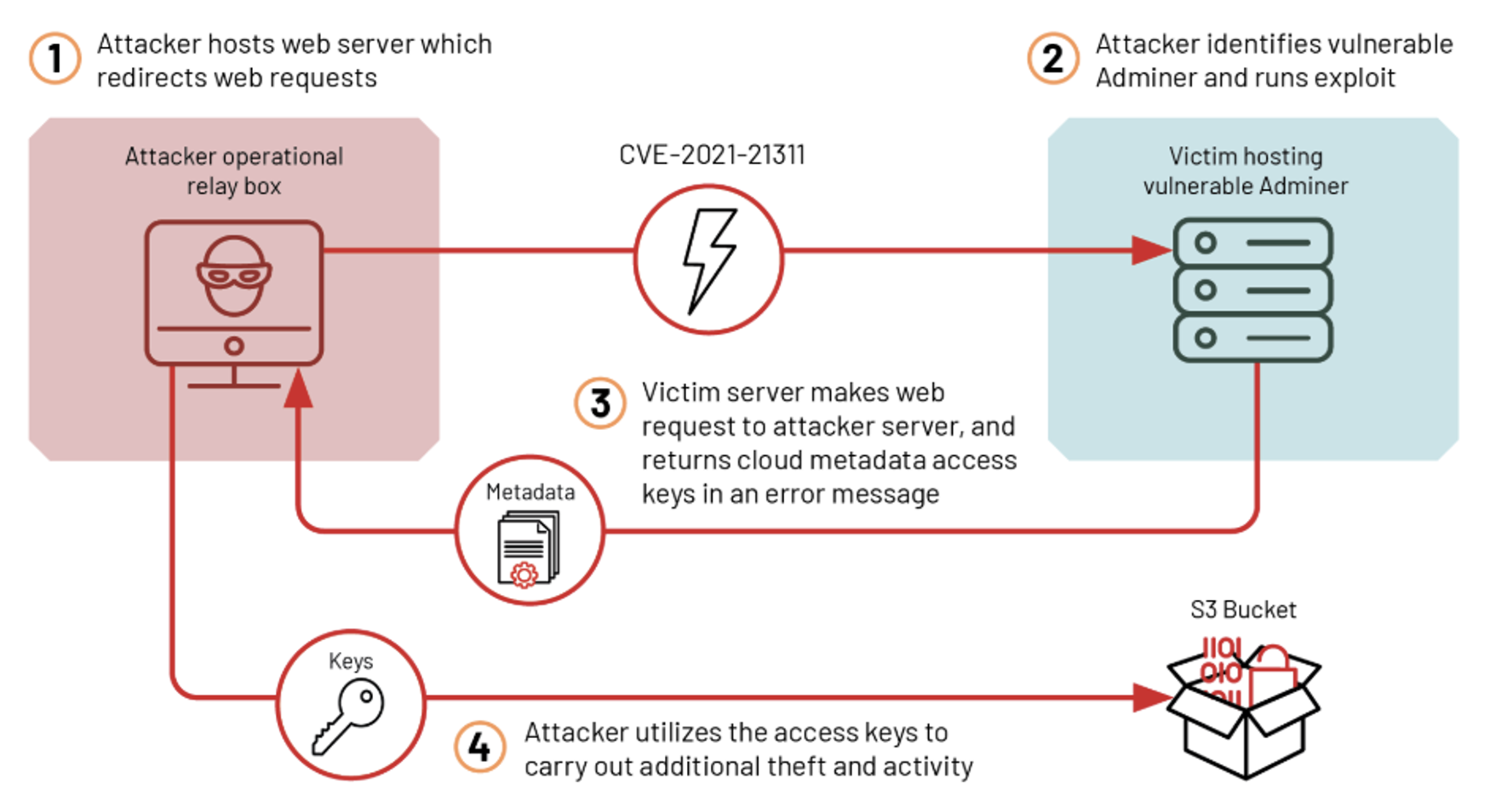
Hunting for Capital One Breach TTPs in AWS logs using Azure Sentinel - Part I - Microsoft Community Hub
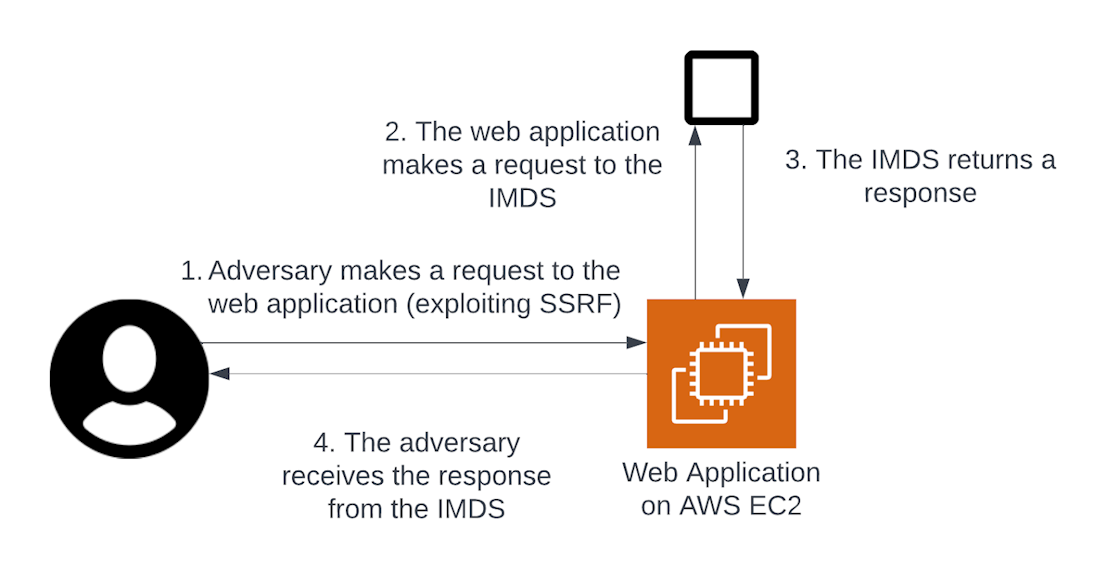
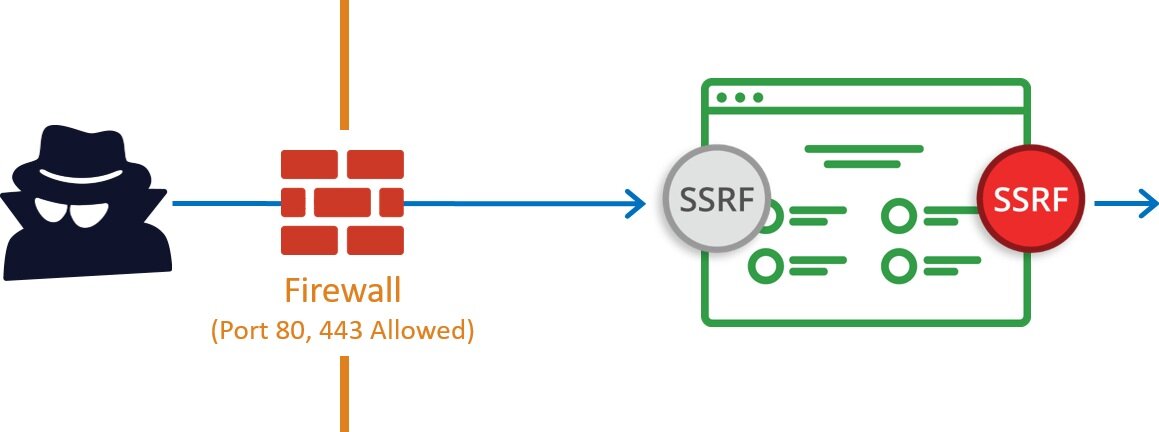
Netflix Cloud Security: Detecting Credential Compromise in AWS | by Netflix Technology Blog | Netflix TechBlog
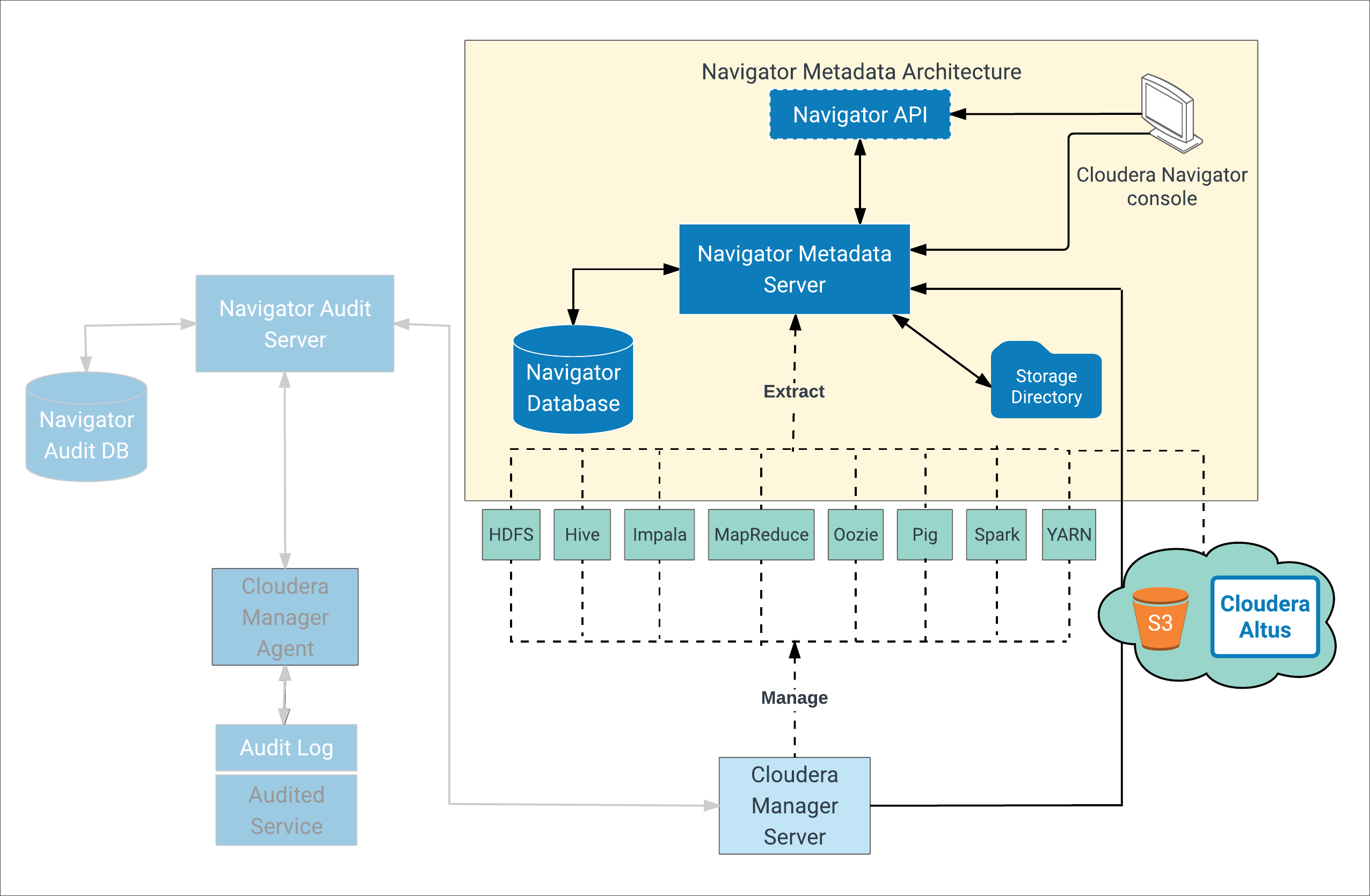
Get started with automated metadata extraction using the AWS Media Analysis Solution | AWS Machine Learning Blog
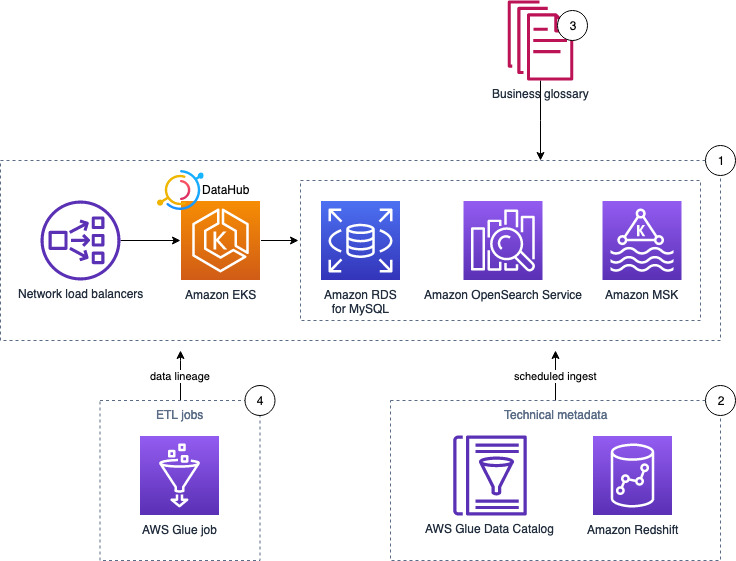
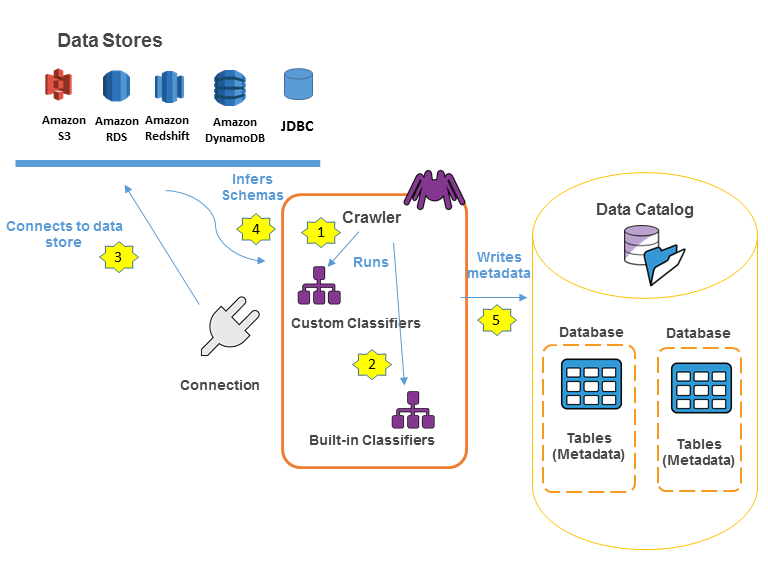
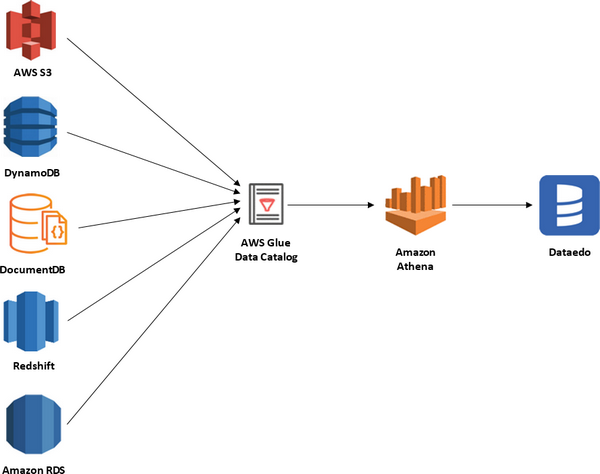
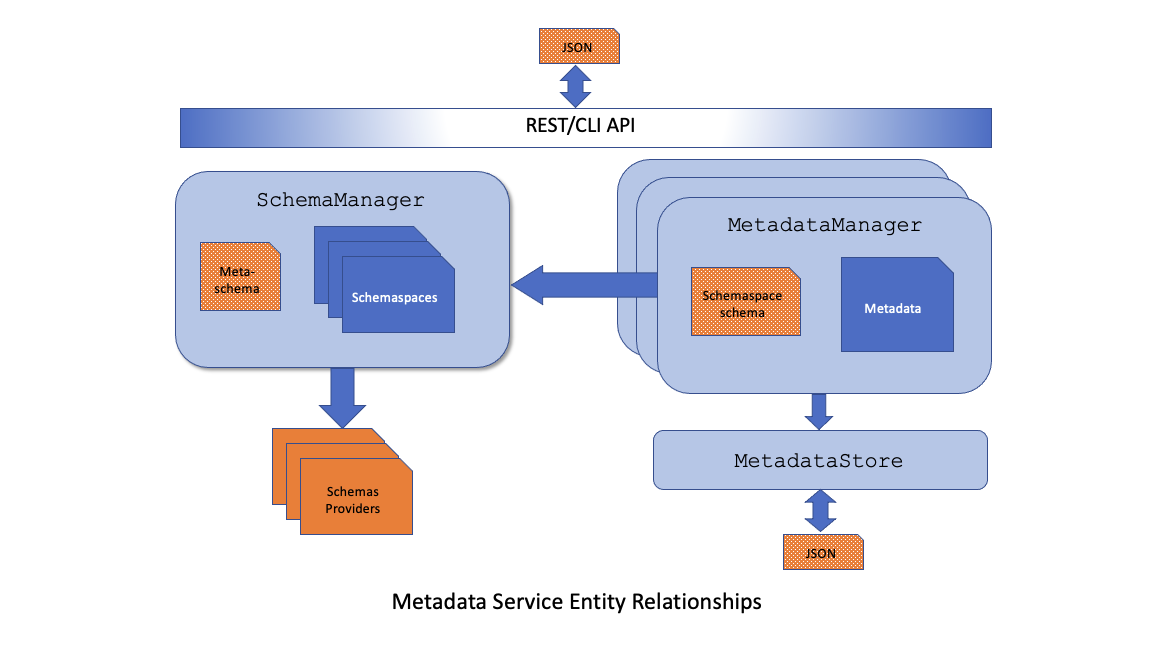
Deploy DataHub using AWS managed services and ingest metadata from AWS Glue and Amazon Redshift – Part 2 | AWS Big Data Blog